Picture Passwords Superiority and Picture Passwords.
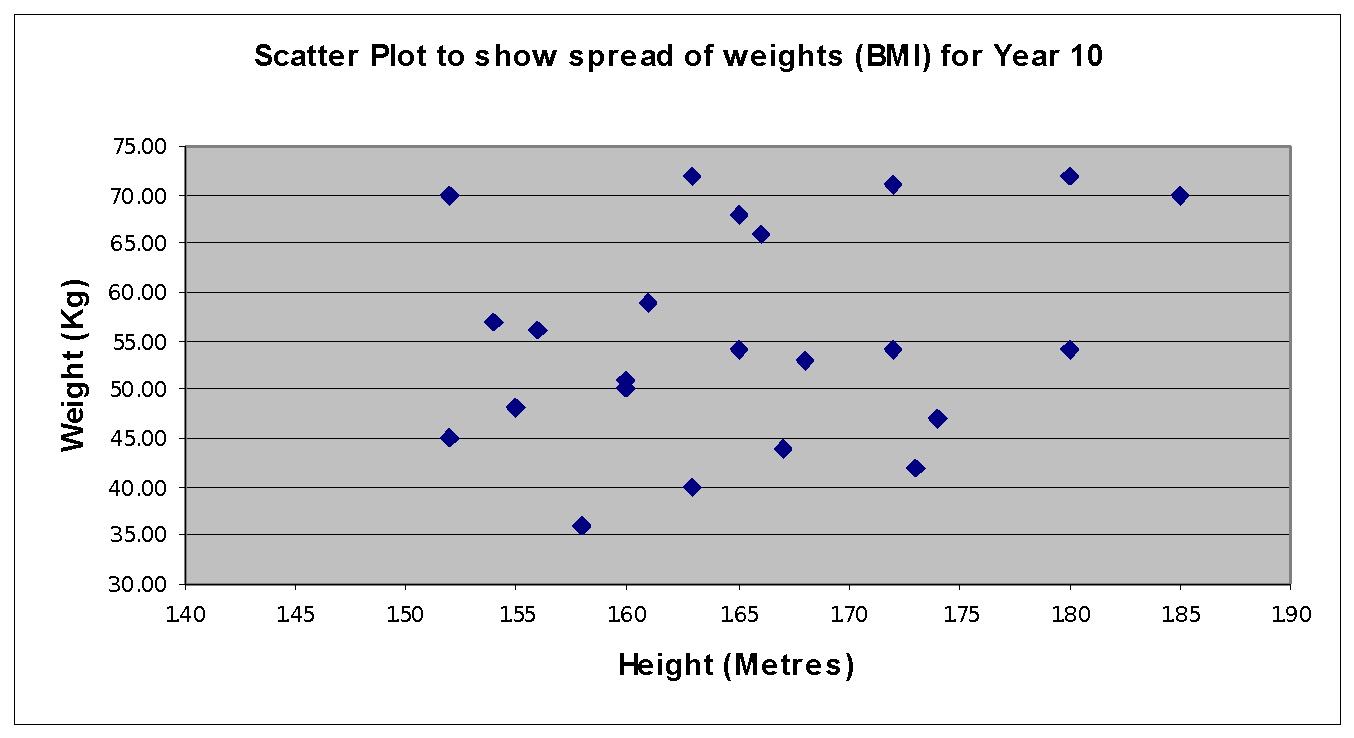
Our paper on the meter design and evaluation won a best paper award at CHI 2017. Password Guessability Service - Our free service for the research community that estimates plaintext passwords' guessability: how many guesses a particular password-cracking algorithm with particular training data would take to guess a password.Using password salts does not make it any more difficult to crack the password for a single user by brute force, but without password salts, it is possible to compute a lookup table for hashes of common passwords in advance. When password hashes are leaked, if a hash value appears in the lookup table, the cracker can recover the corresponding.This paper explores authentication techniques based on pictures as a possible solution to the most important problems concerning traditional passwords. The aim of this work is to bring together the technical (cryptological) and non-technical (psychological) awareness into the research on passwords. Security issues of any authentication mechanism (relying on knowledge) should not be considered.
Welcome to your Password Manager. Easily view and manage passwords you’ve saved in Chrome or Android. Run a Password Checkup to strengthen your security.Research Paper: Information Security Technologies by Benjamin Tomhave November 10, 2004 Prepared for: Professor Dave Carothers EMSE 218 The George Washington University This paper or presentation is my own work. Any assistance I received in its preparation is acknowledged within the paper or presentation, in accordance with academic practice. If I used data, ideas, words, diagrams, pictures.

Reset Your Password. Email Address: Amazing Discounts. 15% OFF. DISCOUNT CODE: RPT15. Get Your Research Paper Written by Experts. You won't find a better deal among professional Services. DISCOUNT CODE: RPT15. Order Now. Get your Research papers in less than 6 Hours. A service built upon trust, reliability, sincerity and professionalism, Research Paper Town specializes in serving learners with.